Protection against cyber attacks is more than just including a capital letter in your password. Here are eight easy ways to improve your cybersecurity on the daily.
1 | Keep your software up to date
We like clicking “Remind me later” on those pesky software update pop-ups as much as the next procrastinator. However, those tragically ignorable updates are a great way to defend against potential cyber violations. A “Software vulnerability” is a weakness or hole in computer security that can be exploited by someone looking to perform unauthorized actions. These vulnerabilities are often targeted for attack by malware that can non-consensually infect your device. Software updates cover these security holes and remove outdated features that are susceptible to being hacked.
A quick turn over of software means that hackers have less time to find the weaknesses of your current software version. You can always turn on automatic updates if you really can’t be bothered with clicking that ‘Update’ button when it pops up on your screen. Just be wary that those software updates are legitimate! (Apparently, nothing is sacred anymore).
2 | Download on the down low
Don’t automatically download attachments from emails; you never know who may get your email and you never know what they’ll put inside. Many hackers like to lace downloads with malware that can be involuntarily installed on your computer. It’s also good practice to be cautious with downloads in general. Don’t download any files unless it’s absolutely necessary. Unnecessary downloads include email signatures, GIFs, and spam attachments.
Some email programs will allow you to automatically download attachments for the emails you receive. While this may save you a bit of time now, it can hurt you in the long run if you need to debug your device in the future. Go with your gut if an email looks fishy. It may be coming from an email that’s “phishing,” using a fake address to deceive recipients into divulging personal details or install malware.
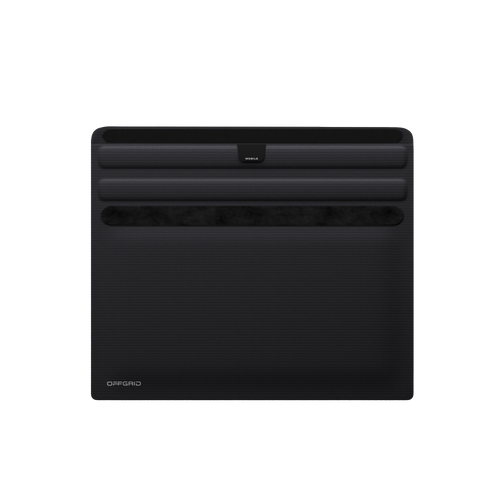
3 | Use an OffGrid Premium Shielding Faraday bag by EDEC
So many tactics to protect against cyber attacks are digital precautions. An EDEC bag is a PHYSICAL guard that’s 100% effective in securing your data. Wireless signals can now be used from remote locations to violate data on devices. EDEC bags use Faraday technology to shield devices from outside signals to prevent data from being altered, added, or deleted when the device is placed inside a sealed bag. They also grant peace of mind to those concerned with the hazards of cell phone radiation, location tracking, or hack attacks. EDEC bags serve as a tangible defense mechanism to ensure data is completely guarded.
4 | Be on your best behavior in public
If you absolutely must use public wifi, networks, or devices, make sure that you are selective about what you do on them. Never enter your credit card information or online bank login on a device or network that does not belong to you. Only share data that you would be comfortable with all of the other people using that network knowing. It is widely recommended that users keep certain digital practices exclusive to private devices. If you want to be extra cautious, you can consider everything you do on a public device or network as public information.
5 | Use a Virtual private network
A virtual private network (VPN) connects your device to a secure server to encrypt data and make it harder for cyber attackers to see what you’re doing online. A VPN server works as a sort of third party that connects to the web on your behalf. Going through the middle man of a VPN increases your anonymity and encrypts your data. Ironically, not all VPNs are super secure so do your research before installation.
6 | Careful with your captions
You may be sharing more than just pictures when you post on Instagram. The more personal information you share, the more vulnerable you are to cyber attacks. People often unintentionally divulge personal details in the captions to their social media posts. Information such as pet names, birth dates, and even home addresses are a few of the many examples of details naively shared online. These personal details are commonly exploited to guess passwords for logins to break into bank or email accounts.
7 | Caution with your network connection
Unsure of the lesser of the two evils between Wifi and Cellular? Cellular networks are typically a pretty safe bet since they usually encrypt your data and authenticate your identity. While there is the occasional exception to this security, you can rely on cellular networks on a regular basis.
Things are a little trickier when it comes to Wifi networks. The security of Wifi networks varies widely. Some Wifi networks will be more secure than cellular, while some can leave you highly exposed to vulnerabilities. If a Wifi network does not require login credentials or a password, it’s usually pretty high risk since hackers can infiltrate unsecured Wifi networks to steal information. Look for private networks, install a VPN (more on that later), and stick to well-known networks that won’t target consumers.
8 | Stay suspicious
Try to adopt a hacker’s mindset when operating in cyberspace. People you don’t suspect in places far away may be trying to get your data for their own benefit. Luckily, there’s no need to go completely off the grid and throw your computer in a lake. Simply being more conscientious of your digital footprint can greatly reduce your chances of a security breach. Be wary of public Wifi networks, when your Bluetooth is on, and what you do on which devices. Aim to log on to personal emails exclusively on your personal devices. Same goes for entering credit card information or personal addresses.
The bad news is that there are, unfortunately, many different ways for hackers to get a hold of your personal data. The good news is that you don’t have to go completely dark to evade a security breach! Many of the dangers typical of cyber attacks can be avoided if you pay attention to avoid possible pitfalls. Practicing caution with your presence in cyberspace is a low risk, high reward way to protect yourself from future cyber attacks. In addition, being mindful of what you do on which devices and networks can drastically reduce your chances of data violations while you’re using the web. Safe surfing!